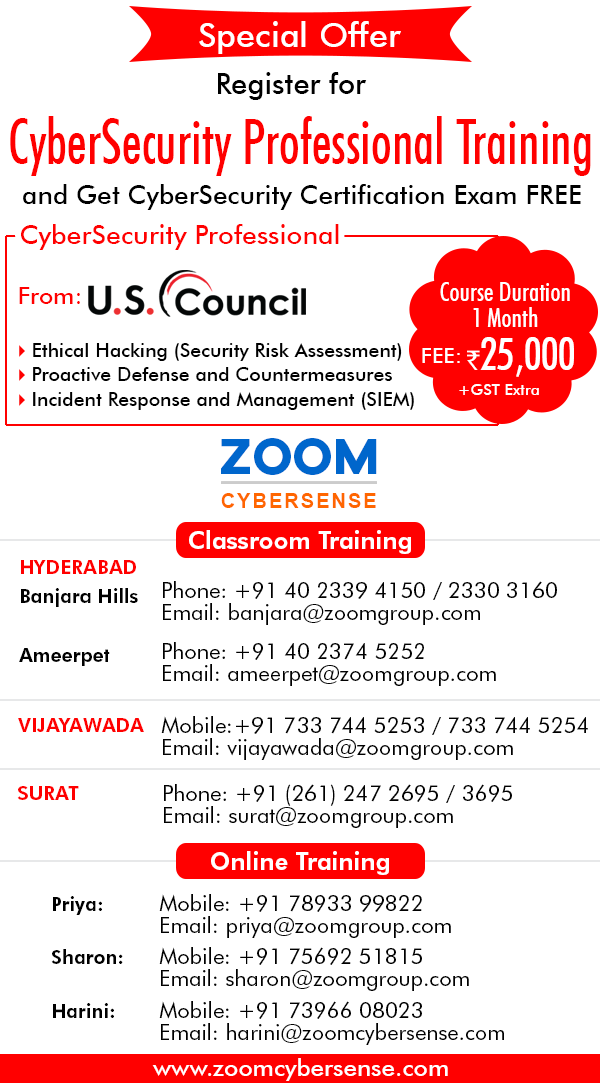
This course is mapped to the popular Cybersecurity Professional Certification Exam from US-Council.
The cybersecurity professional course provides comprehensive training in all aspects of cyber defense methodologies. This course covers the proactive defense mechanisms required of a cybersecurity professional including ethical hacking, firewalls, IPS, vulnerability assessment and cryptography. Vital cybersecurity reactive techniques are also discussed including SIEM, mobile and digital forensics, log analysis and patch management. This course consists of three modules viz
- Security Risk Assessment (Ethical Hacking)
- Proactive Defense and Countermeasures
- Incident Response and Management
A thorough understanding of the underlying principles of networking and operating systems is a prerequisite to pursuing this advanced course. The student is expected to be knowledgeable in IP networks, TCP / IP stack, protocols like http, https, ICMP, ARP, services like DNS, DHCP, LDAP, telnet, ssh as well as routing protocols like RIP, EIGRP, BGP, etc. Expertise in Linux and Windows servers and related technologies is a must.
Key Topics:
- Security Risk Assessment
- Dos and DDos Attacks
- Attack Mitigation Techniques
- Firewalls, IDS, IPS
- Cryptography
- Incident Response and Management
- Log Analysis
- Forensics
The course will cover:
Module 1: Security Risk Assessment (Ethical Hacking)
- What is Hacking
- What is Ethical Hacking
- What is Penetration Testing
- What is Vulnerability Auditing
- What is FootPrinting
- Footprinting Techniques
- Footprinting Website & Tools
- What is Network scanning
- Types of Scanners
- Vulnerability Scanner Tools
- What is a proxy server
- Types of proxies
- What is a Darkweb
- Why hackers prefer to use Darkweb
- What is a web server
- Types of web attacks
- What is session hijacking
- Session hijacking Techniques
- Session hijacking Tools
- What is a DoS and DDoS attack
- DoS attack techniques
- DoS attack Tools
- What is System Hacking
- What is Password Cracking
- Password Cracking techniques
- Password Cracking Website & Tools
- What is a sniffer
- Sniffing Techniques
- Sniffing Tools
- What is Phishing
- Phishing Techniques
- Phishing Tools
- What is malware
- Types of malware
- Malware creation Tools
- USB password stealers
- Types of wireless networks
- Wireless Hacking Techniques
- Wireless Hacking Tools
- What is Kali Linux
- Kali Linux Tools
Module 2: Proactive Defence and Countermeasures
- What is security?
- Layer 1 Security
- Layer 2 Security
- Layer 3 security
- What is a Firewall?
- Types of firewalls
- Designing Security with Firewalls
- NAT
- Security Policy
- Logs Management
- Application Security
- Content / Web Security
- Authentication
- What is VPNs
- Type of VPNs
- GRE
- IPSEC
- SSL
- What is an Intrusion Detection System?
- What is an Intrusion Prevention System?
- OS Hardening
- Patch management
- Antivirus
- Endpoint Security
Module 3: Incident Response and Management
- Introduction to SIEM
- SIEM Architecture
- Events and Logs
- Event Correlation and Event Collection
- Correlation Rules
- Forensic Data
- SIEM Deployment
- Introduction Incident Response
- Incident Response Policy
- Incident Handling
- Forensics of Incident response
- Inside Threat
- Incident Recovery
- Malware Analysis
- Forensic Acquisition of Smartphones
-
- Logical Acquisition
- File System Acquisition
- Physical Acquisition
- Android Forensics
- Retrieving User Activity Information from Android Devices
- iOS (iPhone) Forensics
- Retrieving User Activity Information iOS Devices
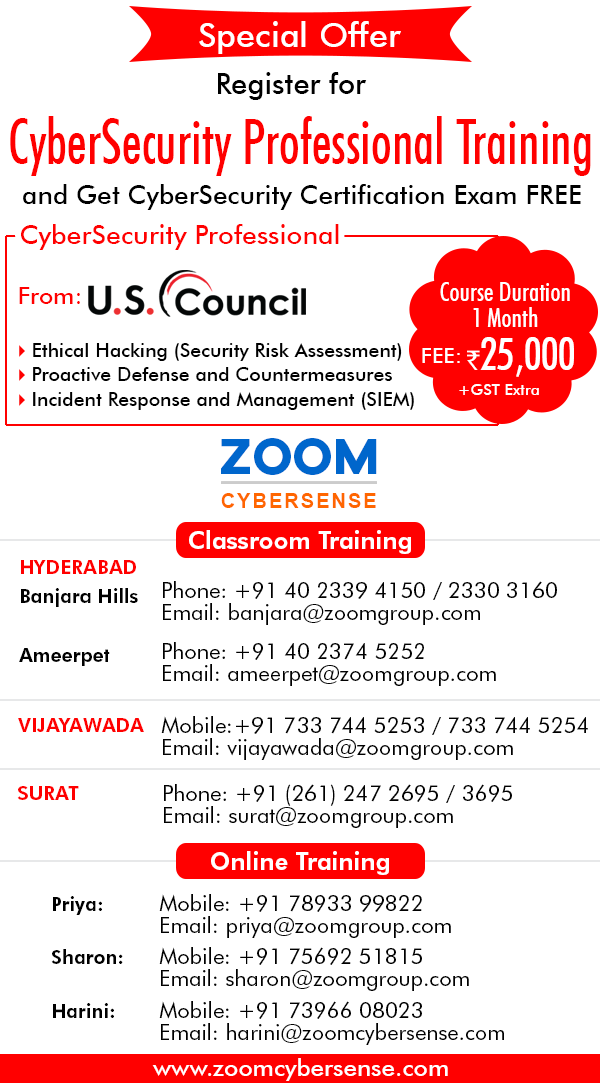
This training course is available in Classroom mode and Online Classroom mode.
Online Classroom Training can be taken from anywhere in the world.
It is an easy way to join a live classroom session. Students can log in from their homes and virtually join the class on Webex. The classroom session will be streamed online for the online classroom subscribers. The instructor will be simultaneously teaching a physical and online classroom. After the session ends, the instructor will take questions from the online classroom students and clarify any doubts.
- Flexibility: Access to attend the course from anywhere via internet - No travel required - cost effective.
- Learning Experience - Online classrooms are an interactive, two-way learning experience.
Kindly contact us at: info@zoomcybersense.com for more details.
Classroom / Online Classroom Schedule
| Date |
Course Outline |
Price |
30th September, 2020
7:30 PM (IST - GMT +5.30)
|
PDF
|
|
31st October, 2020
7:30 PM (IST - GMT +5.30)
|
30th November, 2020
7:30 PM (IST - GMT +5.30)
|